Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Descrição
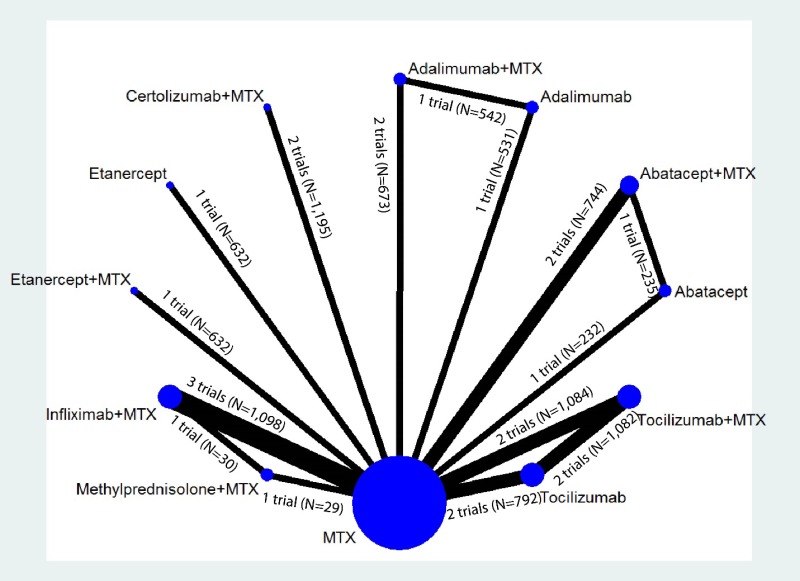
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.
DEF CON 29 - TIB AV-Portal
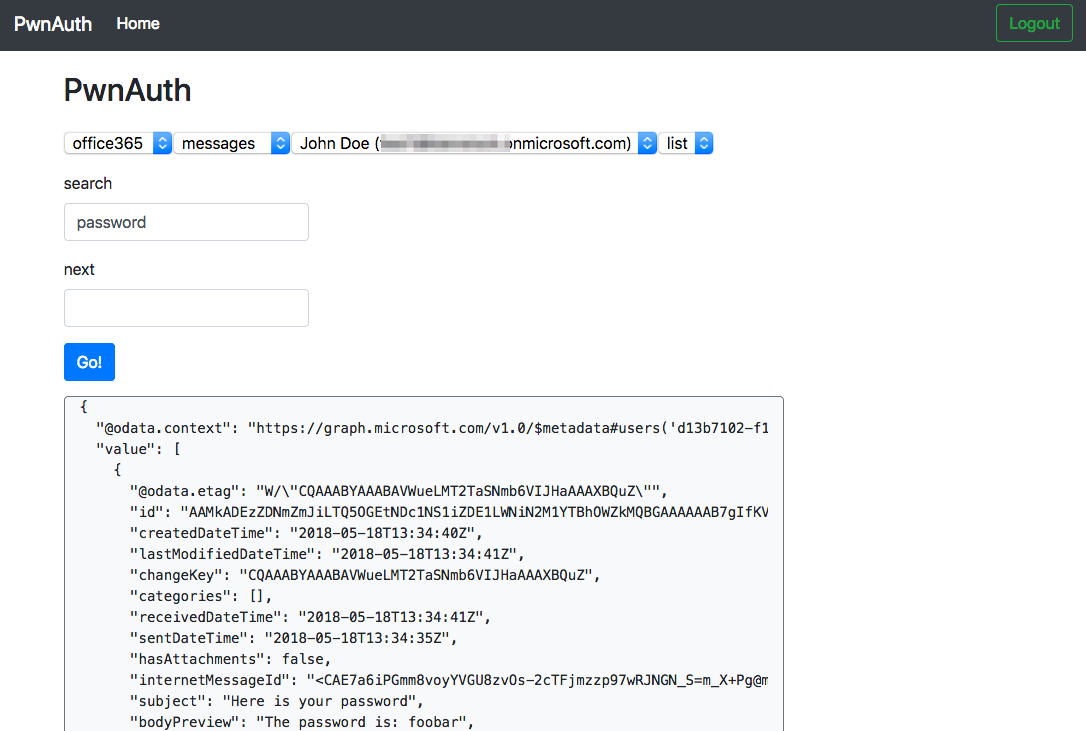
Shining a Light on OAuth Abuse with PwnAuth
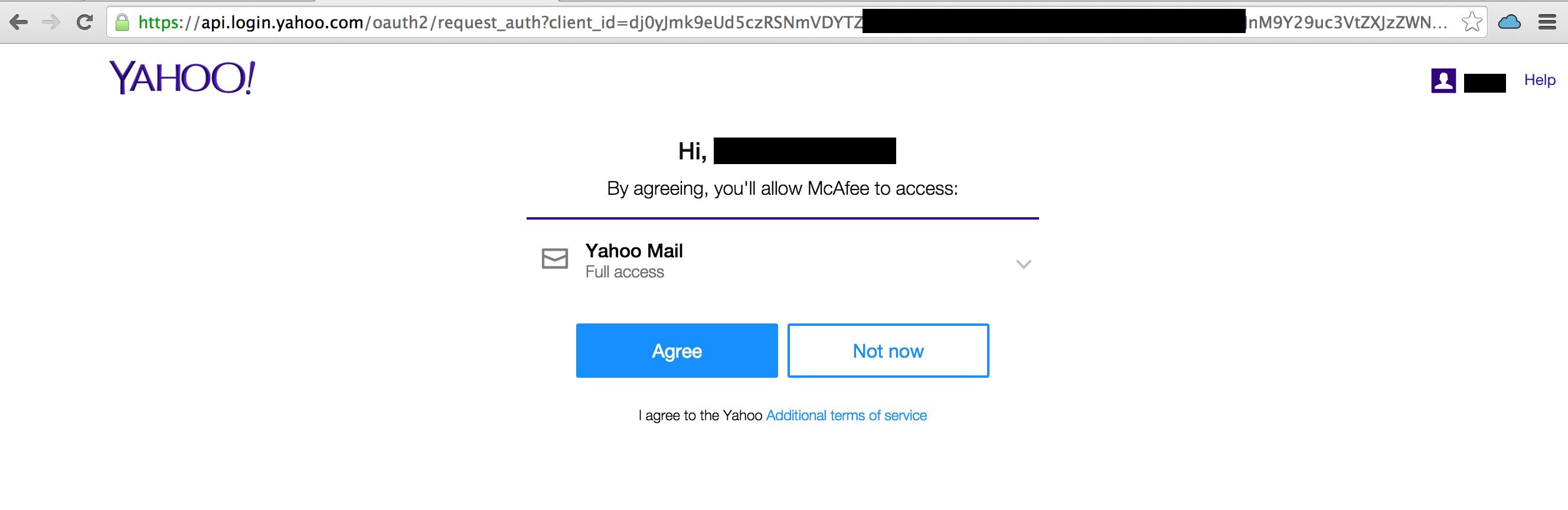
Pawn Storm Abuses OAuth In Social Engineering Attacks

OAuth, Breaking Cybersecurity News
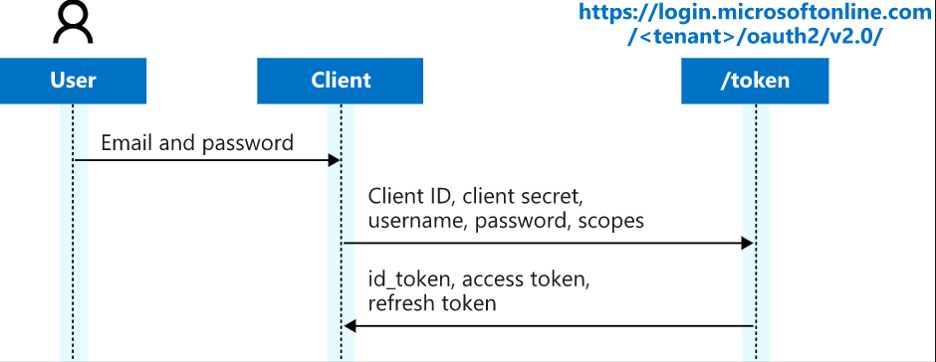
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1

Pawn Storm Mishandles Open Authentication in Advanced Social Engineering Attacks

What is Social Engineering Attacks? ⚔️ Types, Examples.
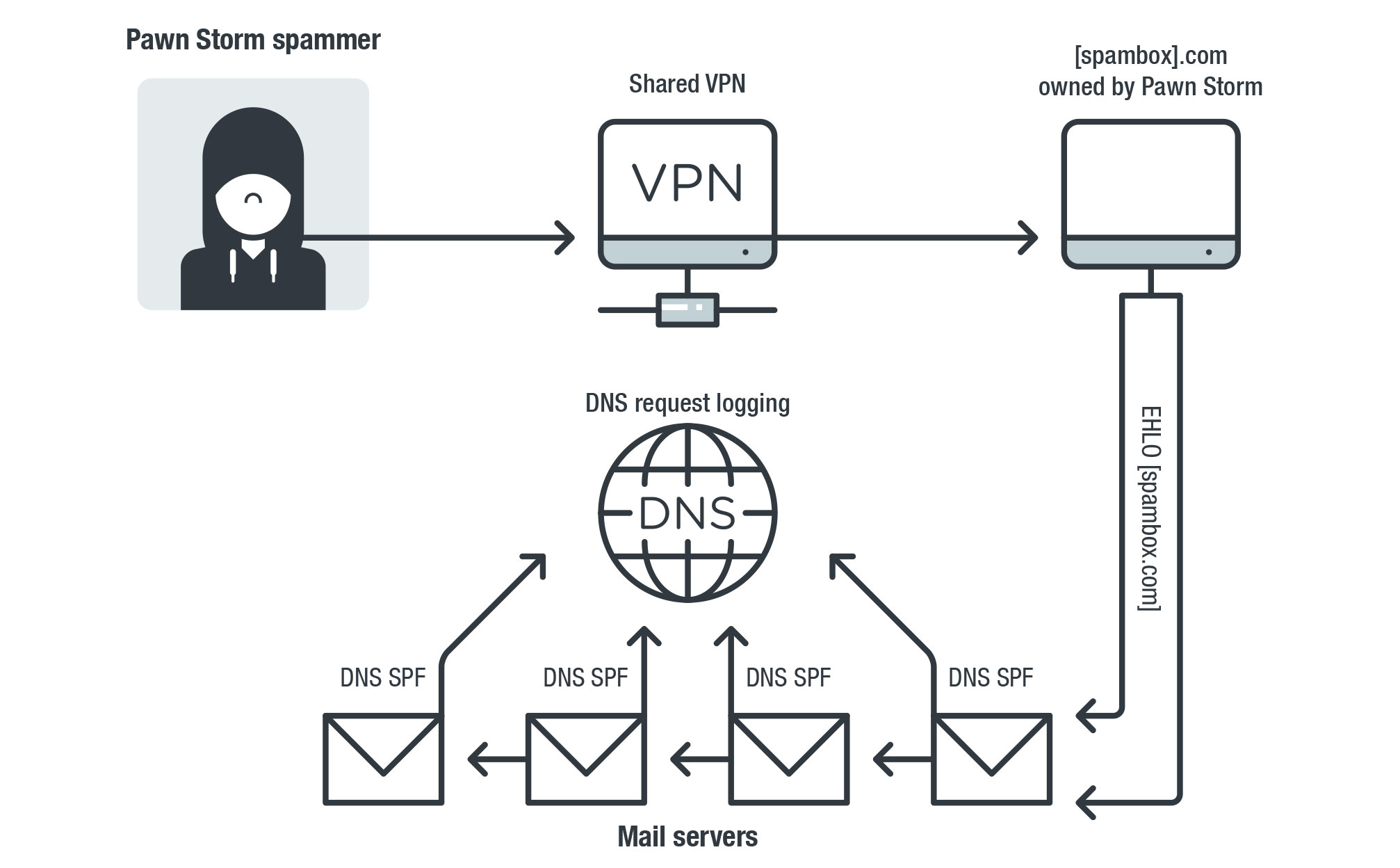
Probing Pawn Storm: Cyberespionage Campaign Through Scanning, Credential Phishing and More - Security News
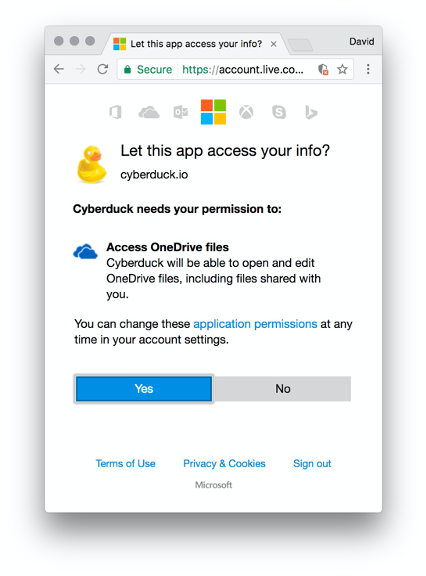
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1
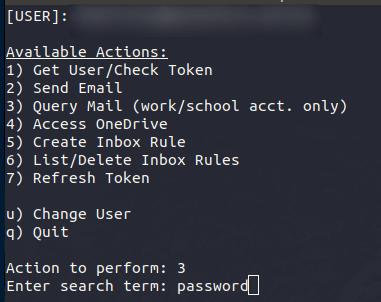
Oauth Token Stealing - Red Team Blog
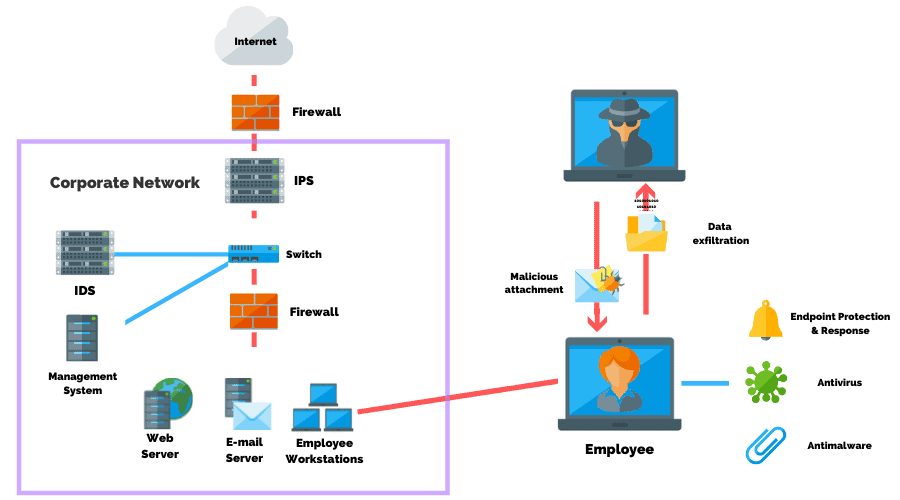
Why Threat Actors Commonly Use Social Engineering Attacks

Social Engineering Attacks & Solutions & Phishing Attacks
GitHub - netskopeoss/phish_oauth: POC code to explore phishing attacks using OAuth 2.0 authorization flows, such as the device authorization grant.
de
por adulto (o preço varia de acordo com o tamanho do grupo)




/cloudfront-us-east-1.images.arcpublishing.com/dmn/XIAJF64GS5A2JNI4OMEQOFQV7Y.jpg)